Keeping your valuable data safe is an absolute priority for us. It’s an obligation that guides everything we do when shaping and powering Nfield’s features. Every conceivable measure is taken to ensure both our team and our software solutions comply with the highest security standards.
Holistic operation
Keeping your data secure depends on a wide range of measures working harmoniously together. A good way to visualize this is to imagine Nfield as a physical office building, where all the different market research and security departments are based. As with all commercial buildings, it is itself protected and complemented with off-site operations.
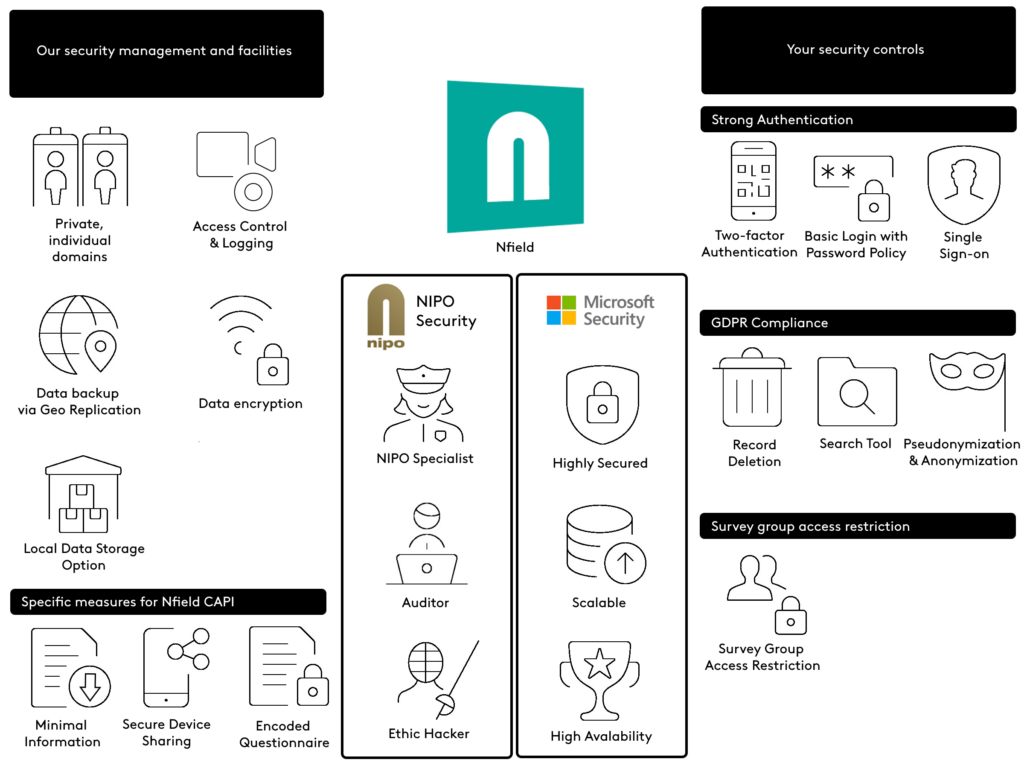
(click image to enlarge)
Data security is underpinned by two core foundations
Our Information Security Management System is ISO 27001:2022 certified. The same as followed by our platform provider, Microsoft.
NIPO security
We maintain a strong security policy that ensures both your data, and our products are safeguarded round the clock. Independent security experts (ethical hackers) scrutinize our security procedures every year to evaluate our tools, processes and people. The measures to conform with ISO 27001:2022 for our Information Security Management System, as certified by an auditor (Auditor), are strictly followed in every wire connection and by every person in our company. As a matter of principle, the smallest possible number of NIPO specialists have access to Nfield’s infrastructure for carrying out deployments and maintenance. See the Nfield Trust Center where you’ll find information about NIPO practices related to security, compliance, and privacy, in the form of documents that can be shared with your clients.
Microsoft security
Nfield runs on Microsoft Azure, the highly secured cloud known for its flawless, trusted performance, extensive data storage and reliability. Microsoft’s engineers work 24/7 to protect the cloud, scale its powers and administer other services which run on it, including Office365. For more information, please visit the Microsoft Trust Center for up-to-date details on policies, processes, and practices that help you manage data control and comply with industry and government regulations.
Your security controls
Nfield provides a number of different features that enable you to secure your domain to the highest level.
Strong Authentication
Two-factor Authentication (2FA): Nfield accounts secured with two-factor authentication require users to enter a code (a token) generated by a standard authenticator app on a mobile phone. This has the effect of complementing something you know (your username and password) with a code obtained through something you have (your phone). It effectively blocks any unauthorized access to your Nfield account, even from those who have obtained your username and password, as these people (or their machines) are unable to retrieve the second factor code from the phone. Your valuable Nfield fieldwork and respondent data is thereby protected from prying eyes. Learn more in our article Protecting your Nfield login with two-factor authentication.
Single-Sign-On (SSO): For enterprises, Nfield can be set up to use Office 365 accounts for Nfield login. Administration of your Nfield user accounts, for as many Nfield domains as you have, is centralized in your organization’s single-sign-on layer. In the case of an employee leaving the organization or other reason for revoking a person’s system access (e.g. because of a security breach), Nfield will automatically be included in the revoked permissions, with immediate effect from when the account in the single-sign-on layer is disabled or reset. With SSO, your password policy for accessing Nfield is automatically aligned with that of your organization.
Strong password policy: Nfield can easily be configured to comply with strong password policies. Domain administrators can set rules for things such as password expiration period, old password re-use and strong password requirements (e.g. minimum number of characters and different character sets). You should also regularly revalidate your authorized users and ensure immediate removal of departing employees.
GDPR compliance toolkit
Survey group access restriction
Surveys contain valuable, and sometimes sensitive, information. It’s therefore essential to restrict access to certain parts of surveys to those who really need it to do their jobs. This is done by assigning users with specific roles which only allow access to designated areas and functionality. Find out more in our article Controlling access to survey rights. Setting the right access also limits the scope of risk in the case of data breach.
Our security management and facilities
The hypothetical building we’ve used to illustrate Nfield’s operation is managed by NIPO, who take care of its security and facilities to ensure compliance with the highest security and privacy standards. Our Information Security Management System is ISO 27001:2022 certified. We have procedures for everything, encrypt your data everywhere, limit access across the board and continuously test for potential security flaws.
Private, individual domains
Your projects are stored in your own individual domain, inaccessible to anyone else – even our employees – unless explicitly requested by you for customer support purposes.
Access control and logging
Nfield allows administrators to configure access on a user-by-user basis, defining the scope of activities every user is allowed to perform. Password requirements can also be set to enforce your chosen password policy, however strong you need it to be. All user actions are tracked and domain administrators can review them individually. The system automatically signs users out when inactive for more than 15 minutes.
Data backup
Your collected data is stored in secure Microsoft SQL database servers and replicated in other data centers so it can be restored in the event of something going wrong. Microsoft security policies strictly regulate access to its data centers.
Data encryption
All your data is secured by SSL and encrypted, both at rest and during transfer, to protect it from sniffing.
Local data storage option
Different countries and industries often have their own specific regulations when it comes to data storage. To comply with this, market research companies need to give careful consideration to where their respondent data is stored. To enable data storage compliance, we have developed the ability to separate survey deployment from storage of respondent data. This means it is now possible, for example, to deploy a survey from the Hong Kong SAR Microsoft Data Center and store the respondent data in the Singapore Microsoft Data Center. Find out more in our article Local Data Storage Compliance, around the World.
Specific measures for Nfield CAPI
Tablet devices are desirable prizes for thieves. Their thin, lightweight nature also makes them easy to forget about and accidentally leave behind. Nfield therefore also deploys additional measures to limit the extent of data exposure risk due to being locally stored on a mobile device.
Minimal information
Nfield ensures the minimum amount of information possible is present on any mobile device at any given moment. Each device is only sent the surveys and associated respondent information specifically assigned to its user(s). Data that no longer needs to be accessible is removed as soon as possible.
- You control which surveys and respondent details are assigned to each interviewer, so can limit exposure.
- Survey response data is transferred to a local, encrypted database and removed from the device as soon as possible after each interview is completed. (As soon as the interviewer connects to internet network.)
- Upon completion of each interviewer’s involvement, all information relating to a project is deleted from their device as soon as you unassign them or close the project (once the interviewer has connected to the internet and synchronized their device with the Nfield system).
Secure device sharing
The same mobile device can be shared by multiple interviewers. Each survey and its collected data is only accessible to the relevant interviewer, via their login credentials. Interviewers cannot review, start or modify any surveys not specifically assigned to them.
Encoded questionnaires
Nfield questionnaires are stored in an encoded proprietary format. The original script is never displayed in an interviewer’s device, so interviewers cannot make changes.
Get our full security whitepaper
We ❤ secure solutions
Fully compliant practices, means you can rest assured when it comes to data security. And with cloud-based operation delivering unbeatable cost-efficiency together with all the capacity you need, whenever you need it, Nfield is the ultimate solution for improving both your quality of work and your profit margins.